The Essential Cybersecurity Guide for Startups: Protecting Your Business Growth & Digital Transformation
In the dynamic landscape of modern business, startups often prioritize rapid innovation and aggressive market penetration. However, the foundational element enabling sustained business growth and digital transformation for any emerging enterprise is a robust cybersecurity posture. This essential cybersecurity guide for startups is meticulously crafted to equip new businesses with actionable strategies, best practices, and a comprehensive understanding of how to protect their invaluable digital assets, ensure data privacy, and safeguard their reputation from an ever-evolving array of cyber threats. For startups, where resources are often finite and agility is paramount, understanding unique challenges and implementing cost-effective, scalable security solutions is not merely a technical requirement, but a strategic imperative that secures competitive advantage and fosters investor confidence.
Understanding Cybersecurity in the Startup Ecosystem
For startups, cybersecurity is more than just IT overhead; it’s an intrinsic component of their operational resilience and a key enabler of long-term success. Unlike established corporations with extensive budgets and dedicated security teams, emerging businesses navigate a unique set of challenges:
- Limited Resources: Financial constraints often mean smaller security budgets and fewer specialized personnel.
- Rapid Scaling: Fast-paced growth can lead to overlooked security gaps in infrastructure and processes.
- Focus on Innovation: The drive to quickly develop and deploy new products or services sometimes inadvertently sidelines security considerations.
- Attractive Targets: Startups, particularly those with innovative intellectual property or significant customer data, can be lucrative targets for cybercriminals.
This section of our comprehensive cybersecurity guide for startups delves into these specific contextual factors, highlighting why a proactive and integrated approach to security is crucial from day one, laying a secure foundation for future digital transformation initiatives.
Why Cybersecurity is a Growth Enabler, Not Just a Cost
Effective cybersecurity actively contributes to a startup’s growth and competitive edge. By mitigating risks, it directly safeguards the core tenets of business development. Robust security measures protect intellectual property, ensuring that innovative ideas remain proprietary. They build and maintain customer trust, which is invaluable for user adoption and retention. Furthermore, a strong security stance enhances investor confidence, signalling a mature and responsible approach to business operations. Consider these compelling benefits:
- Reputation Protection: A single data breach can irreversibly damage a startup’s nascent brand and market perception. Proactive cybersecurity safeguards public image.
- Legal & Regulatory Compliance: Adhering to data protection laws avoids hefty fines and legal battles that can cripple a young company.
- Operational Continuity: Preventing cyberattacks minimizes downtime, ensuring that critical business operations remain uninterrupted, thus sustaining productivity.
- Competitive Advantage: Startups demonstrating superior security can differentiate themselves in the market, attracting security-conscious clients and partners.
The Digital Footprint of a Modern Startup
A startup’s digital footprint often expands rapidly, encompassing a complex array of assets and interactions. Understanding this footprint is the first step in protecting it. This includes:
- Cloud Infrastructure: Most startups leverage cloud services (AWS, Azure, GCP) for everything from data storage to application hosting. Securing these environments is paramount.
- Employee Devices: Laptops, smartphones, and other endpoints used by employees, especially in remote or hybrid work models, represent potential entry points for attackers.
- Third-Party Vendors: Startups increasingly rely on SaaS tools and external service providers, expanding their attack surface to include supply chain vulnerabilities.
- Proprietary Data: Customer information, financial records, product designs, and trade secrets are all high-value targets for theft or compromise.
Each of these elements requires specific security considerations, which we will explore in subsequent sections to help startups build a comprehensive defense.
Identifying Key Cybersecurity Risks for Emerging Businesses
This section of our comprehensive cybersecurity guide for startups is dedicated to pinpointing the specific threats and vulnerabilities that emerging businesses, focused on rapid ‘business growth and digital transformation,’ must proactively address to prevent costly disruptions. Understanding the threat landscape is foundational to developing an effective security strategy. Startups are often perceived as “soft targets” due to their perceived lack of sophisticated defenses, making them particularly susceptible to a range of attack vectors.
What are the most common cyber threats facing startups?
Cybercriminals frequently target startups using well-known, yet highly effective, methods. Recognizing these threats is the initial step in developing robust protection strategies. Here are some of the most prevalent:
- Phishing and Social Engineering: Attackers use deceptive emails, messages, or websites to trick employees into revealing sensitive information (passwords, financial data) or downloading malware. This remains a leading cause of data breaches.
- Malware and Ransomware: Malicious software can infiltrate systems to steal data, disrupt operations, or encrypt files until a ransom is paid. Ransomware attacks, in particular, can halt a startup’s entire operation, leading to significant financial loss and reputational damage.
- Cloud Misconfigurations: While cloud services offer scalability and flexibility, incorrect configurations of security settings, access controls, or storage buckets can expose sensitive data to the public internet.
- DDoS (Distributed Denial of Service) Attacks: These attacks overwhelm a startup’s servers or network with a flood of traffic, making their website or services unavailable to legitimate users.
- Web Application Vulnerabilities: Flaws in custom-built or third-party web applications can create entry points for attackers to inject malicious code, steal data, or gain unauthorized access.
- Intellectual Property Theft: For innovative startups, proprietary code, algorithms, designs, and business plans are critical assets. Cybercriminals or state-sponsored actors may target these for competitive advantage.
Beyond External Threats: Insider Vulnerabilities & Supply Chain Risks
While external threats dominate headlines, startups must also contend with risks originating from within their own organization and through their network of partners:
- Insider Threats: These can be malicious (e.g., a disgruntled employee stealing data) or accidental (e.g., an employee falling for a phishing scam or mishandling sensitive information). Both scenarios pose significant risks to data integrity and privacy.
- Supply Chain Vulnerabilities: Startups rely heavily on third-party software, cloud providers, payment processors, and other vendors. A security flaw or breach in one of these partners can directly impact the startup, creating a cascading risk. Thorough vendor risk management is crucial.
The following table summarizes common cybersecurity risks and their potential impact on a startup’s critical operations and growth trajectory:
| Risk (Entity) | Description (Attribute) | Primary Impact on Startup Growth (Attribute) | Key Mitigation Strategy (Attribute) |
|---|---|---|---|
| Phishing | Deceptive communication to trick users into revealing sensitive data. | Data breaches, financial loss, reputational damage, operational disruption. | Employee security awareness training, email filtering, MFA. |
| Ransomware | Malware encrypts data, demanding payment for decryption. | Extended downtime, significant financial cost, data loss, irreversible reputational harm. | Regular data backups (off-site), endpoint protection, incident response plan. |
| Data Breach | Unauthorized access to or exposure of sensitive, protected, or confidential data. | Loss of customer trust, regulatory fines, legal liabilities, IP theft, competitive disadvantage. | Data encryption, access control, vulnerability management, security audits. |
| Cloud Misconfiguration | Incorrectly set up cloud security controls leading to vulnerabilities. | Data exposure, unauthorized access, service disruption, compliance failures. | Automated configuration checks, IAM best practices, security architecture review. |
| Insider Threat | Malicious or accidental actions by current or former employees/partners. | Data theft, system sabotage, espionage, intellectual property compromise. | Access controls (least privilege), monitoring, employee training, data loss prevention (DLP). |
| DDoS Attack | Overwhelming a server or network with traffic, causing service outage. | Loss of revenue, reputational damage, customer dissatisfaction, operational paralysis. | DDoS mitigation services, robust network infrastructure, traffic filtering. |
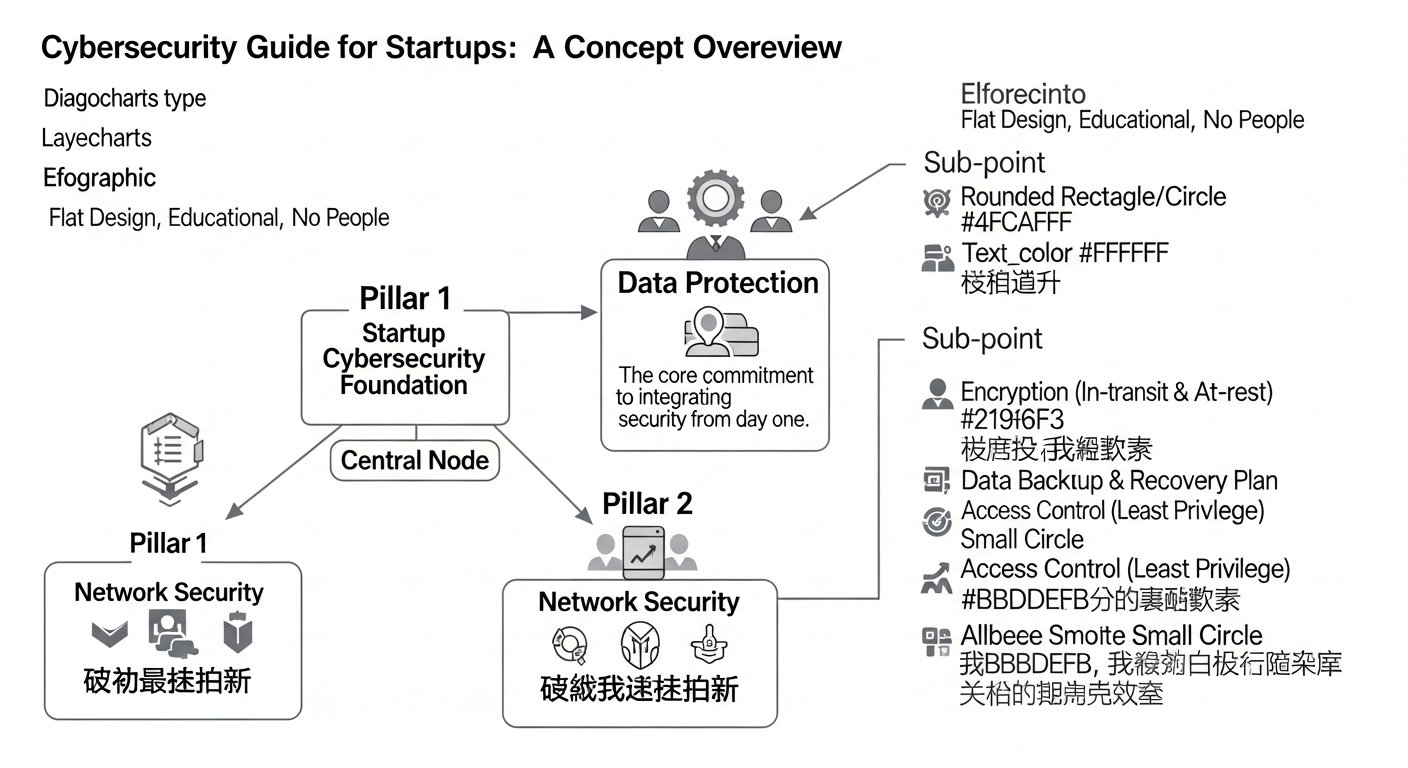
[INLINE IMAGE 1: place after second H2]
Building a Foundational Cybersecurity Strategy for Startups
Having established the foundational elements of a robust cybersecurity posture and identified potential threats, it’s now critical for startups to translate this awareness into a coherent, actionable strategy. This section of our cybersecurity guide for startups outlines how to build a security framework that not only protects current operations but also scales with your ‘business growth and digital transformation,’ ensuring security is embedded rather than bolted on.
The Pillars of a Robust Security Posture
A strong cybersecurity strategy for startups is built upon well-established principles, often summarized by frameworks like the CIA triad and defense-in-depth:
- Confidentiality, Integrity, Availability (CIA Triad):
- Confidentiality: Protecting sensitive information from unauthorized access (e.g., encryption, access controls).
- Integrity: Ensuring data is accurate and has not been tampered with (e.g., checksums, version control).
- Availability: Guaranteeing authorized users can access systems and data when needed (e.g., backups, disaster recovery).
- Defense-in-Depth: This approach involves layering multiple security controls to protect against failure of any single measure. Think of it like a castle with multiple walls, moats, and guards – if one defense is breached, others stand ready. This includes physical, technical, and administrative controls.
- Principle of Least Privilege: Granting users and systems only the minimum necessary access rights required to perform their tasks. This drastically limits the potential damage from a compromised account.
- Zero Trust Architecture: A modern security model that dictates “never trust, always verify.” Every user, device, and application attempting to access resources must be continuously authenticated and authorized, regardless of whether they are inside or outside the traditional network perimeter.
Crafting a Startup-Specific Security Policy
Even small startups benefit immensely from documented security policies. These guidelines formalize expectations, provide clear instructions, and serve as a reference for employees and new hires. A comprehensive security policy for a startup should address:
- Acceptable Use Policy: Defines how employees can use company resources (devices, networks, software) for work-related and personal activities.
- Access Control Policy: Specifies who can access what data and systems, and under what conditions. This includes guidelines for password strength, multi-factor authentication (MFA), and regular access reviews.
- Data Handling Policy: Outlines how sensitive data should be collected, stored, processed, transmitted, and disposed of in compliance with relevant regulations.
- Incident Response Plan: A crucial document detailing steps to take before, during, and after a cybersecurity incident to minimize damage and restore operations.
- Employee Security Awareness Training Policy: Commits to regular training to educate employees on recognizing threats and following security best practices.
- Vendor Security Policy: Establishes criteria for evaluating and managing the security posture of third-party service providers.
Developing these policies need not be overly complex. Startups can leverage templates from organizations like NIST (National Institute of Standards and Technology) or CISA (Cybersecurity and Infrastructure Security Agency) and adapt them to their specific operational context and budget constraints.
Implementing Essential Cybersecurity Measures for Digital Protection
Moving beyond strategic planning, this section of our cybersecurity guide for startups focuses on the practical implementation of key measures that directly safeguard your digital assets and foster secure ‘business growth and digital transformation.’ These are the concrete steps that every startup can and should take to build a resilient defense against cyber threats.
Data Breach Prevention Strategies: Technical Controls
Implementing effective technical controls forms the backbone of any robust cybersecurity strategy. These measures actively protect systems and data from unauthorized access and compromise:
- Multi-Factor Authentication (MFA): Implement MFA across all critical systems (email, cloud services, internal applications). Requiring a second form of verification (e.g., a code from a phone, a biometric scan) drastically reduces the risk of account compromise, even if passwords are stolen.
- Data Encryption: Encrypt sensitive data both “at rest” (stored on servers, databases, laptops) and “in transit” (when being sent over networks). This ensures that even if data is intercepted or accessed without authorization, it remains unreadable.
- Firewalls and Network Segmentation: Deploy firewalls to monitor and control incoming and outgoing network traffic, blocking malicious connections. Segmenting your network separates different parts of your infrastructure, limiting an attacker’s lateral movement if one segment is breached.
- Regular Software Updates and Patch Management: Keep all operating systems, applications, and firmware updated. Software vendors frequently release patches to fix newly discovered vulnerabilities. Neglecting updates leaves glaring security holes.
- Secure Access Control: Implement robust identity and access management (IAM) systems. This includes strong password policies, regular review of user permissions, and immediate revocation of access for departing employees.
- Data Backup and Recovery: Regularly back up all critical data to secure, off-site locations. Test your recovery procedures periodically to ensure you can quickly restore operations after a data loss event, whether from an attack or system failure.
- Endpoint Detection and Response (EDR): Deploy EDR solutions on all employee devices and servers. EDR actively monitors endpoints for suspicious activity, detects threats, and can automate response actions.
Employee Security Awareness Training: Your First Line of Defense
Technology alone cannot secure a startup; employees are often the weakest link if untrained, but the strongest defense if properly educated. Consistent security awareness training is indispensable:
- Regular Training Sessions: Conduct mandatory training for all employees, covering topics like phishing recognition, password best practices, data handling, and reporting suspicious activity.
- Simulated Phishing Attacks: Periodically send simulated phishing emails to test employee vigilance and identify areas for further training. This provides practical, real-world experience without actual risk.
- Culture of Security: Foster an environment where employees feel comfortable reporting security concerns without fear of reprisal. Encourage a proactive security mindset throughout the organization.
How can startups implement cost-effective security solutions?
Budget constraints are a reality for many startups, but effective cybersecurity doesn’t always require massive investment. Smart choices can yield significant protection:
- Leverage Cloud-Native Security Features: Cloud providers (AWS, Azure, GCP) offer extensive built-in security tools and services that are often more cost-effective than deploying on-premise solutions.
- Open-Source Tools: Many reputable open-source security tools for vulnerability scanning, penetration testing, and network monitoring can be utilized with minimal licensing costs.
- Focus on Basics First: Prioritize foundational security measures like MFA, strong passwords, regular backups, and employee training, as they provide the highest ROI for preventing common attacks.
- Outsource Expertise (CISO-as-a-Service): For specialized needs, consider fractional or CISO-as-a-Service models, providing expert guidance without the cost of a full-time executive.
- Security as a Service (SaaS): Many security vendors offer SaaS solutions that reduce upfront investment and management overhead, providing services like email security, endpoint protection, and vulnerability scanning on a subscription basis.
Here is a table summarizing essential cybersecurity measures and their impact:
| Measure (Entity) | Description (Attribute) | Implementation Priority (Attribute) | Cost-Effectiveness (Attribute) | Impact on Digital Transformation (Attribute) |
|---|---|---|---|---|
| Multi-Factor Authentication (MFA) | Adds an extra layer of security beyond passwords. | High | High (often free/low cost) | Significantly reduces account takeover risks, enabling secure cloud adoption. |
| Employee Security Training | Educates staff on cyber threats and best practices. | High | High (internal resources/low-cost platforms) | Empowers human firewall, reducing social engineering success, fostering secure culture. |
| Data Encryption | Scrambles sensitive data to protect it from unauthorized access. | High | Moderate (tools built into OS/cloud) | Secures data at rest and in transit, crucial for compliance and IP protection. |
| Regular Data Backups | Creates copies of data for recovery in case of loss or attack. | High | High (cloud storage/automated solutions) | Ensures business continuity, critical for ransomware recovery, mitigates data loss impact. |
| Incident Response Plan | Pre-defined steps to handle, contain, and recover from a cyberattack. | High | Moderate (time investment for planning) | Minimizes breach impact, accelerates recovery, maintains customer trust during crises. |
| Secure Access Control | Manages who has access to which resources based on identity and role. | High | High (IAM tools, least privilege) | Limits damage from compromised credentials, supports scalable user management. |
[INLINE IMAGE 2: place after fourth H2]
Navigating Compliance and Data Privacy for Startup Growth
In the age of pervasive data, legal and ethical obligations surrounding data privacy are non-negotiable for any business, especially for startups aiming for global ‘business growth and digital transformation.’ This section of our cybersecurity guide for startups illuminates the critical landscape of compliance and data privacy, highlighting why adherence is not just about avoiding fines, but about building trust and market credibility.
Understanding Key Data Protection Regulations
Depending on their target markets, data types, and operational locations, startups may need to comply with various regional and industry-specific regulations. Non-compliance can lead to severe penalties, reputational damage, and loss of customer trust. Key regulations include:
- General Data Protection Regulation (GDPR): A European Union law governing data protection and privacy for all individuals within the EU and EEA. It has extraterritorial reach, meaning any startup processing data of EU citizens, regardless of their location, must comply.
- California Consumer Privacy Act (CCPA) / California Privacy Rights Act (CPRA): Landmark privacy laws in the United States, granting California consumers extensive rights over their personal information and requiring businesses to be transparent about data practices.
- Health Insurance Portability and Accountability Act (HIPAA): If your startup handles protected health information (PHI) in the United States, strict compliance with HIPAA’s privacy and security rules is mandatory.
- Payment Card Industry Data Security Standard (PCI DSS): Any startup that stores, processes, or transmits credit card information must adhere to PCI DSS to protect cardholder data. While not a law, it’s a contractual obligation enforced by credit card brands.
- Children’s Online Privacy Protection Act (COPPA): If your startup’s online services or products are directed at children under 13 and collect personal information, COPPA compliance is essential.
Understanding the scope and requirements of these regulations is paramount for a startup’s legal standing and ethical operation.
Building Privacy-by-Design into Startup Operations
Integrating privacy into the core design of systems and business practices, rather than as an afterthought, is known as Privacy-by-Design. This proactive approach benefits startups by:
- Minimizing Data Collection: Only collecting the data absolutely necessary for a specific purpose (data minimization).
- Embedding Privacy Controls: Designing systems with privacy settings as default, giving users control over their data.
- Transparency: Being clear and transparent with users about what data is collected, why, and how it’s used through easily understandable privacy policies.
- Data Subject Rights: Establishing clear processes for users to exercise their rights (e.g., access, rectification, erasure of their data).
- Secure Data Processing Agreements (DPAs): When engaging third-party vendors who process data on your behalf, ensuring robust DPAs are in place that clearly outline data protection responsibilities.
Embracing privacy-by-design from the outset can save startups significant time, cost, and legal exposure down the line, fostering consumer trust and enabling smoother market entry.
The following table provides a quick overview of key cybersecurity compliance regulations relevant to startups:
| Regulation (Entity) | Scope (Attribute) | Key Requirements (Attribute) | Relevance for Startups (Attribute) |
|---|---|---|---|
| GDPR (EU) | Data privacy for EU/EEA residents. | Consent, data subject rights (access, erasure), data protection impact assessments, breach notification, data minimization. | Crucial if serving EU customers or operating in the EU. Non-compliance risks significant fines. |
| CCPA/CPRA (CA, US) | Data privacy for California residents. | Right to know, delete, opt-out of sale/sharing of personal information, non-discrimination. | Applicable to many US-based startups handling data of California residents, especially those exceeding revenue/data thresholds. |
| HIPAA (US) | Protection of Protected Health Information (PHI). | Privacy Rule, Security Rule, Breach Notification Rule for covered entities and business associates. | Essential for health-tech or medical startups dealing with patient data. |
| PCI DSS | Security standard for credit card data. | Build/maintain secure network, protect cardholder data, maintain vulnerability management, strong access control, regular monitoring/testing. | Mandatory for any startup processing, storing, or transmitting credit card information, regardless of size. |
Scaling Cybersecurity with Your Startup’s Evolution
As a startup experiences accelerated ‘business growth and digital transformation,’ its cybersecurity needs inevitably evolve. What worked for a small team in a single office will likely be insufficient for a rapidly expanding workforce, diverse cloud infrastructure, and growing customer base. This section of our cybersecurity guide for startups focuses on the critical strategies for scaling cybersecurity effectively, ensuring that security matures in tandem with the business.
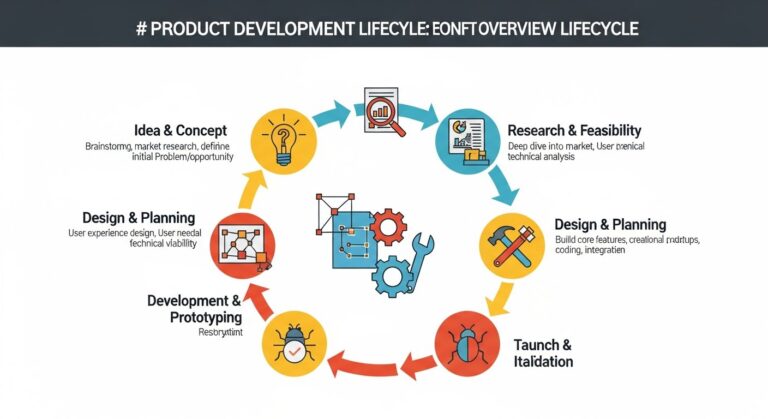
Why is an incident response plan crucial for business continuity?
While prevention is paramount, no security posture is entirely impregnable. Cyberattacks are an unfortunate reality, and how a startup responds can dictate its survival. An incident response plan (IRP) is not merely a reactive document; it’s a proactive blueprint for business continuity:
- Minimizes Damage: A well-defined IRP enables rapid detection, containment, and eradication of threats, limiting data loss, financial impact, and operational downtime.
- Restores Operations Faster: Clear steps for recovery mean systems and services can be brought back online efficiently, reducing revenue loss and customer frustration.
- Maintains Trust: A transparent and effective response demonstrates competence to customers, investors, and regulatory bodies, helping to preserve reputation.
- Legal & Compliance Obligation: Many data protection regulations (like GDPR) mandate timely breach notification and a structured response.
A typical IRP should include:
- Preparation: Defining roles, responsibilities, communication channels, and necessary tools.
- Identification: Detecting and confirming the security incident.
- Containment: Isolating affected systems to prevent further spread.
- Eradication: Removing the threat from the environment.
- Recovery: Restoring systems and data to normal operations.
- Post-Incident Review: Analyzing what happened, how the response performed, and implementing lessons learned to improve future security.
Advanced Security: Frameworks, Audits, and Cyber Insurance
As startups mature, they often look to adopt more structured approaches to cybersecurity management:
- Security Frameworks: Adopting recognized frameworks like NIST Cybersecurity Framework or ISO 27001 provides a comprehensive, structured approach to managing security risks. These frameworks help formalize processes, identify gaps, and demonstrate due diligence.
- Security Audits and Penetration Testing: Regular external security audits and penetration tests (ethical hacking) by independent experts help identify vulnerabilities that internal teams might miss. These assessments provide an objective view of your security posture.
- Vendor Risk Management (VRM): As reliance on third-party vendors grows, formalizing VRM becomes crucial. This involves assessing the security practices of your suppliers, ensuring their security measures align with your own, and including security clauses in contracts.
- Cyber Insurance: Investing in cyber insurance can provide financial protection against the costs associated with data breaches, ransomware attacks, and other cyber incidents (e.g., legal fees, regulatory fines, notification costs, business interruption). It’s a critical component of risk transfer.
- CISO-as-a-Service (Fractional CISO): For growing startups that need executive-level security leadership but aren’t ready for a full-time Chief Information Security Officer, a fractional CISO can provide strategic guidance, framework implementation, and ongoing risk management expertise.
Each of these advanced measures helps startups mature their security capabilities, ensuring that protection keeps pace with their dynamic business development and expanding digital footprint.
Common Cybersecurity Mistakes Startups Make (and How to Avoid Them)
Having established the foundational elements of a robust cybersecurity posture and strategies for scaling, it’s equally important for startups to understand the common pitfalls that can derail their security efforts and impede their digital transformation. By learning from frequent missteps, emerging businesses can proactively strengthen their defenses.
The Cost of Overlooking Basic Security
Many startups, in their zeal for rapid innovation and lean operations, unfortunately overlook fundamental security practices, leading to avoidable and costly breaches. The primary mistakes include:
- Neglecting Employee Training: Believing that technical tools alone suffice, companies often skip or minimize security awareness training, leaving employees vulnerable to social engineering.
- Default Passwords and Weak Credentials: Failure to change default passwords on new devices or services, or allowing weak, easily guessable passwords, creates immediate entry points for attackers.
- Lack of Data Backups: Not regularly backing up critical data, or failing to test recovery procedures, makes a startup extremely vulnerable to data loss from attacks or system failures.
- Ignoring Software Updates: Delaying or skipping patches for operating systems, applications, and firmware leaves known vulnerabilities unaddressed, which attackers actively exploit.
- No Incident Response Plan: Without a clear plan for reacting to a cyberattack, startups can suffer prolonged downtime, increased financial losses, and greater reputational damage.
- Insufficient Cloud Security Configuration: Assuming cloud providers handle all security, leading to misconfigured S3 buckets, exposed databases, or lax access controls in cloud environments.
- Poor Vendor Security Vetting: Integrating third-party tools or services without adequately assessing their security posture introduces significant supply chain risk.
Learning from Common Breaches: Startup Cyberattack Case Studies
While specific startup names are often not publicly disclosed for privacy reasons, common attack vectors highlight the dangers of these mistakes:
- Phishing Leading to Account Takeover: A startup loses control of its primary social media account or email system after an employee falls for a sophisticated phishing scam, resulting in reputational damage and potential loss of customer data.
- Ransomware on Unpatched Servers: A fast-growing tech startup experiences a complete shutdown of its operations for days, and loses critical customer data, because a public-facing server had an unpatched vulnerability that allowed ransomware to encrypt its systems.
- Cloud Data Exposure due to Misconfiguration: A SaaS startup inadvertently exposes a database containing sensitive user information to the public internet because an AWS S3 bucket was not properly secured, leading to massive fines and loss of trust.
These scenarios underscore that the cost of neglecting basic cybersecurity measures far outweighs the investment in proactive protection, directly impeding a startup’s journey towards sustainable digital transformation.
The Future of Cybersecurity: Trends for Growing Startups
As startups continue their journey of ‘business growth and digital transformation,’ the cybersecurity landscape will continue to evolve at an accelerated pace. Staying abreast of emerging trends is vital for maintaining a resilient security posture. This final section of our cybersecurity guide for startups offers a forward-looking perspective on key developments that will shape security strategies for emerging businesses in the coming years.
AI, Automation, and Proactive Threat Detection
Artificial intelligence (AI) and machine learning (ML) are rapidly transforming cybersecurity, offering powerful capabilities that can significantly benefit startups:
- Automated Threat Detection: AI-powered security tools can analyze vast amounts of data in real-time to detect anomalous behavior and identify emerging threats (e.g., new malware variants, sophisticated phishing attempts) much faster than human analysts.
- Predictive Analytics: ML algorithms can predict potential attack vectors and vulnerabilities by learning from past incidents and threat intelligence, allowing startups to proactively strengthen their defenses.
- Automated Incident Response: AI can automate routine incident response tasks, such as isolating compromised devices or blocking malicious IP addresses, speeding up response times and reducing the burden on limited security teams.
- Behavioral Analytics: AI can establish baselines of normal user and system behavior, making it easier to spot deviations that might indicate an insider threat or compromised account.
For startups, leveraging AI-driven security solutions, often available as SaaS platforms, can provide enterprise-grade protection without requiring extensive in-house expertise or large capital expenditure. This enables them to scale their security more efficiently as they grow.
Zero Trust and Supply Chain Security Evolution
Two other critical trends will continue to gain prominence:
- Expanded Zero Trust Adoption: The “never trust, always verify” principle of Zero Trust will become even more pervasive. Startups will increasingly implement granular access controls, continuous authentication, and micro-segmentation, treating every access attempt – whether from inside or outside the traditional network perimeter – with suspicion. This is particularly relevant for startups with remote workforces and distributed cloud environments.
- Enhanced Supply Chain Security: With the increasing interconnectedness of digital ecosystems, supply chain attacks (where an attacker compromises a trusted third-party vendor to gain access to their clients) pose a significant threat. Startups will need to implement more rigorous vendor risk management programs, demanding higher security standards from their partners and leveraging tools for continuous monitoring of third-party security posture. This includes comprehensive software bill of materials (SBOM) to understand components and potential vulnerabilities within their software supply chain.
- Privacy-Enhancing Technologies (PETs): As data privacy regulations become stricter, startups will increasingly adopt PETs like differential privacy, homomorphic encryption, and federated learning to process and analyze sensitive data while minimizing privacy risks.
By proactively integrating these future-oriented security trends into their strategic planning, startups can build highly resilient and adaptive cybersecurity defenses, positioning themselves for secure and sustainable innovation and growth in the digital era.
In conclusion, establishing a robust cybersecurity posture from the earliest stages is not merely a defensive measure but a strategic enabler for any startup pursuing ambitious business growth and digital transformation. This comprehensive cybersecurity guide for startups has outlined the critical steps, from understanding unique risks and building foundational strategies to implementing practical measures, navigating compliance, and scaling security with your evolution. By prioritizing cybersecurity, startups safeguard their digital assets, protect their intellectual property, build invaluable customer and investor trust, and ensure uninterrupted innovation. The journey of a startup is fraught with challenges, but a proactive, intelligent approach to cybersecurity ensures that digital threats do not become insurmountable barriers to success.