Zero Trust Security Model Explained 2026: Your Startup’s Non-Negotiable Defense Strategy
The digital landscape for startups in 2026 is a paradox: unprecedented opportunity married with escalating threat. Gone are the days when a robust perimeter firewall was sufficient. Cybercriminals are more sophisticated, breaches are more frequent, and the cost of compromise has never been higher, impacting not just finances but also reputation, investor confidence, and even regulatory standing. For ambitious founders building the next big thing, the question isn’t if you’ll face a cyberattack, but when, and how prepared you are. This is where the Zero Trust security model moves from a theoretical best practice to an absolute necessity. It’s a fundamental shift from the outdated “trust but verify” mindset to “never trust, always verify” – a proactive, data-centric approach essential for safeguarding your innovation in a world without perimeters.
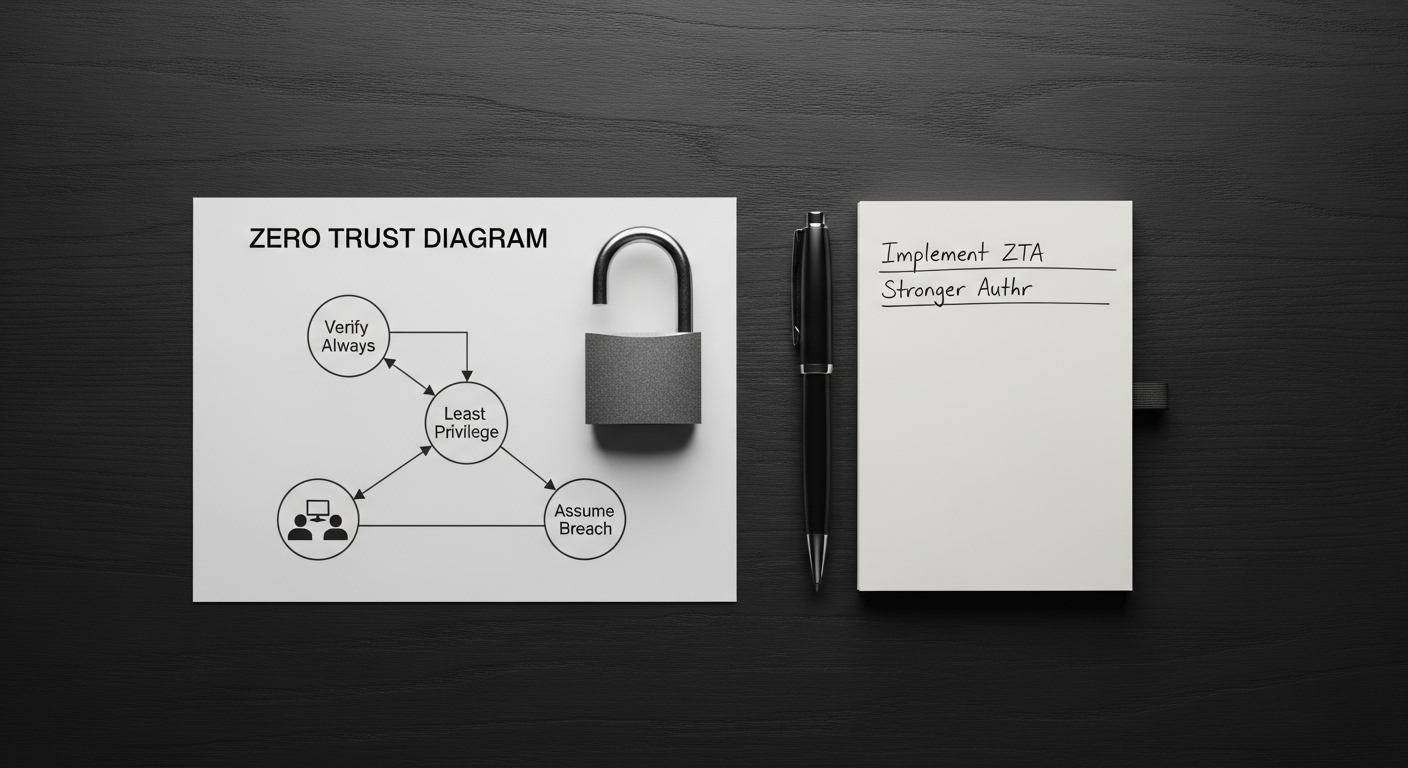
The Core Tenets of Zero Trust: Trust Nothing, Verify Everything
At its heart, Zero Trust is a strategic initiative that prevents successful data breaches by eliminating the concept of implicit trust from an organization’s network architecture. It mandates that no user, device, or application – whether inside or outside the traditional network perimeter – is inherently trustworthy. Every access request must be authenticated, authorized, and continuously validated before access is granted. This paradigm shift is built upon several foundational principles:
- Never Trust, Always Verify: This is the golden rule. Every access request, regardless of origin, is treated as if it’s coming from an untrusted network. Verification is mandatory for all users, devices, and applications.
- Least Privilege Access: Users and devices are granted only the minimum access privileges necessary to perform their tasks, and only for the duration required. This drastically limits the potential damage if an account or device is compromised.
- Microsegmentation: The network is divided into small, isolated segments, each with its own security controls. This prevents lateral movement of attackers within the network, containing breaches to a tiny fraction of the infrastructure. For instance, a finance application might be isolated from the marketing database, even if both reside on the same cloud platform.
- Continuous Monitoring and Authentication: Trust is never granted indefinitely. User and device identities, contexts (location, time of day), and behaviors are continuously monitored. If conditions change (e.g., a user attempts to access sensitive data from an unusual location), re-authentication or additional verification steps are triggered.
- Device Posture Assessment: Before granting access, devices are rigorously checked for security compliance – ensuring they have up-to-date patches, antivirus software, and meet defined security policies. A non-compliant device is either blocked or quarantined until issues are resolved.
Unlike traditional perimeter security, which focuses on keeping external threats out while implicitly trusting everything inside the network, Zero Trust assumes threats can originate from anywhere – internal or external. This makes it inherently more resilient against modern attack vectors, including sophisticated phishing campaigns, insider threats, and supply chain compromises that bypass traditional defenses.
Why Zero Trust is a Must-Have for Startups in 2026
The urgency for Zero Trust adoption among startups in 2026 isn’t just about keeping up with trends; it’s about survival and competitive advantage. Here’s why this model is non-negotiable for your ambitious venture:
- Escalating Cybercrime Costs: Cyberattacks are not just a nuisance; they are a multi-trillion-dollar global industry. Recent reports indicate that the average cost of a data breach for small to medium-sized businesses can range from hundreds of thousands to millions of dollars when factoring in downtime, remediation, reputational damage, and legal fees. For a startup, such a hit can be existential. Zero Trust significantly reduces the attack surface and mitigates the impact of a breach.
- Regulatory Compliance and Investor Confidence: As your startup scales, compliance with regulations like GDPR, CCPA, HIPAA, and SOC 2 becomes critical. Zero Trust principles – such as least privilege, data segmentation, and continuous monitoring – directly support these compliance frameworks. Demonstrating a proactive, robust security posture also significantly boosts investor confidence and can be a differentiator in competitive funding rounds. Investors are increasingly scrutinizing security practices as part of their due diligence.
- The Remote/Hybrid Work Imperative: The shift to remote and hybrid work models is permanent for many startups. Employees access critical resources from various locations, using diverse devices, often outside traditional corporate networks. Perimeter-based security is simply irrelevant in this distributed environment. Zero Trust ensures that every access request, whether from a coffee shop or the office, is equally scrutinized, securing your distributed workforce.
- Cloud-Native Architectures and SaaS Dependency: Startups thrive on agility, leveraging cloud platforms (AWS, Azure, GCP) and SaaS applications (Salesforce, HubSpot, Slack) extensively. These services inherently extend your attack surface beyond your control. Zero Trust is designed for these dynamic, multi-cloud environments, providing consistent security policies across all your digital assets, regardless of where they reside.
- Protection Against Sophisticated Attacks: Modern threats like ransomware, advanced persistent threats (APTs), and supply chain attacks often involve initial compromise of a seemingly innocuous endpoint, followed by extensive lateral movement within the network. Zero Trust’s microsegmentation and continuous verification stop attackers in their tracks, preventing them from escalating privileges or reaching high-value data.
- Reduced Risk of Insider Threats: While often overlooked, insider threats—whether malicious or accidental—can be devastating. Zero Trust’s least privilege and continuous monitoring policies minimize the potential for unauthorized access or data exfiltration by employees, contractors, or partners.
By adopting Zero Trust, you’re not just buying a security product; you’re investing in a strategic framework that future-proofs your startup against an ever-evolving threat landscape, builds trust with your customers and partners, and protects your most valuable assets: your data and your innovation.
The Pillars of a Robust Zero Trust Architecture
Implementing Zero Trust isn’t a single product purchase; it’s a holistic architectural shift requiring integration across multiple security domains. For startups, this means strategically leveraging a combination of technologies and processes. Here are the core pillars you’ll need to build your Zero Trust environment:
- Identity & Access Management (IAM) and Multi-Factor Authentication (MFA):
- Purpose: The cornerstone of Zero Trust. Ensures only verified users and devices can access resources.
- Key Components:
- Single Sign-On (SSO): Streamlines user access while enforcing policies.
- Multi-Factor Authentication (MFA): Adds layers of verification beyond just a password (e.g., biometrics, hardware tokens, authenticator apps).
- Adaptive Authentication: Adjusts authentication strength based on context (location, device, time).
- Tools to Consider: Okta Identity Cloud, Duo Security (Cisco), Auth0 (Okta), Microsoft Entra ID (formerly Azure AD).
- Endpoint Security (EDR/XDR):
- Purpose: Continuously assess the security posture of every device (laptops, mobile phones, servers) attempting to access resources.
- Key Components:
- Endpoint Detection and Response (EDR): Monitors endpoint activity, detects threats, and enables rapid response.
- Extended Detection and Response (XDR): Integrates EDR with other security layers (network, cloud, email) for broader visibility.
- Device Posture Checks: Verifies OS updates, antivirus status, configuration compliance before granting access.
- Tools to Consider: CrowdStrike Falcon, SentinelOne Singularity, Microsoft Defender for Endpoint.
- Network Segmentation & Microsegmentation:
- Purpose: Isolate critical assets and limit lateral movement of threats within your network.
- Key Components:
- Software-Defined Segmentation: Uses policies to dynamically segment networks, rather than static VLANs.
- Micro-Perimeters: Creates small, granular security zones around individual applications or workloads.
- Zero Trust Network Access (ZTNA): Provides secure, direct-to-app access, replacing traditional VPNs.
- Tools to Consider: Zscaler Private Access (ZPA), Cloudflare Zero Trust, Palo Alto Networks Prisma Access, Illumio.
- Data Security:
- Purpose: Protect sensitive data at rest, in transit, and in use.
- Key Components:
- Data Loss Prevention (DLP): Prevents sensitive information from leaving controlled environments.
- Encryption: Encrypts data wherever it resides.
- Data Classification: Identifies and labels sensitive data to apply appropriate controls.
- Tools to Consider: Microsoft Purview Information Protection, Varonis Data Security Platform.
- Visibility & Analytics (SIEM/SOAR):
- Purpose: Gain comprehensive insights into security events, detect anomalies, and automate responses.
- Key Components:
- Security Information and Event Management (SIEM): Collects, aggregates, and analyzes log data from across your infrastructure.
- Security Orchestration, Automation, and Response (SOAR): Automates incident response workflows.
- Threat Intelligence Platforms (TIP): Provides context on known threats and vulnerabilities.
- Tools to Consider: Splunk Enterprise Security, Elastic Security (SIEM), IBM QRadar.
- Cloud Security Posture Management (CSPM):
- Purpose: Ensure continuous security and compliance for your cloud environments.
- Key Components:
- Configuration Drift Detection: Identifies deviations from desired security configurations.
- Compliance Auditing: Checks cloud resources against regulatory frameworks.
- Vulnerability Management: Scans for misconfigurations and vulnerabilities in cloud assets.
- Tools to Consider: Palo Alto Networks Prisma Cloud, Wiz, Orca Security.
For a startup, the key is to prioritize and integrate. Start with strong IAM/MFA and robust endpoint security, then expand into network segmentation and cloud security as your infrastructure matures.
Implementing Zero Trust: A Phased Approach for Startups
Adopting Zero Trust might seem daunting, but it’s an iterative journey, not a single destination. For startups, a phased, strategic approach is key to achieving robust security without overwhelming resources.
Phase 1: Foundation & Discovery (Weeks 1-8)
- Define Your Protect Surface: This is the most critical first step. Identify your “crown jewels” – the data, applications, assets, and services (DAAS) that are absolutely vital to your business. This could be customer data, source code, financial records, or your core SaaS application. Don’t try to secure everything at once.
- Action: Conduct workshops with key stakeholders (product, engineering, legal, finance) to map out critical DAAS. Categorize by sensitivity and business impact.
- Map Transaction Flows: Understand how users, devices, and applications interact with your identified DAAS. Who needs access to what, when, and from where? Document these flows.
- Action: Use network monitoring tools (e.g., firewall logs, cloud flow logs) and interviews to visualize data paths.
- Assess Current State & Identify Gaps: Evaluate your existing security controls against Zero Trust principles. What IAM, endpoint, or network segmentation tools do you already have? Where are the biggest vulnerabilities in your DAAS access paths?
- Action: Inventory existing security tools. Perform a basic risk assessment against your DAAS.
Phase 2: Initial Implementation & Policy Creation (Months 2-6)
- Strengthen Identity & Access Management (IAM) with MFA: This is often the quickest win and provides significant security uplift. Implement strong MFA for all users, especially for privileged accounts. Migrate to SSO where possible.
- Action: Deploy an MFA solution (e.g., Duo, Okta Verify) across all critical applications. Integrate with your identity provider (e.g., Google Workspace, Microsoft Entra ID).
- Implement Endpoint Security & Device Posture Checks: Ensure all corporate devices are managed, have EDR/XDR protection, and meet baseline security requirements before being granted access.
- Action: Deploy an EDR solution (e.g., CrowdStrike) to all employee laptops. Implement basic device compliance policies (e.g., OS updates, disk encryption).
- Pilot Microsegmentation for a Critical DAAS: Choose one high-value application or dataset and implement granular access policies. This could involve using a ZTNA solution to control access to your internal development environment or a specific SaaS application.
- Action: Select a pilot DAAS. Implement a ZTNA solution (e.g., Cloudflare Zero Trust, Zscaler Private Access) to restrict access to only authorized users and devices.
- Architect Zero Trust Policies: Based on your defined protect surface and transaction flows, create granular, attribute-based access control (ABAC) policies. These policies should consider identity, device posture, location, time, and application context.
- Action: Document clear “who, what, when, where, why, how” policies for accessing your pilot DAAS.
Phase 3: Expansion & Continuous Improvement (Months 6+)
- Expand Microsegmentation: Gradually extend microsegmentation to other critical DAAS, progressively reducing your network’s attack surface.
- Action: Roll out ZTNA to more internal applications. Consider network segmentation within your cloud environments.
- Enhance Data Security: Implement DLP solutions where necessary and ensure sensitive data is encrypted at rest and in transit.
- Action: Identify locations of sensitive data and enforce encryption. Explore DLP for critical data repositories.
- Implement Robust Visibility & Analytics: Centralize security logging (SIEM) to gain a holistic view of your security posture and detect anomalies.
- Action: Set up a SIEM solution (e.g., Splunk Cloud, Elastic Cloud) to ingest logs from all critical systems.
- Monitor & Improve Continuously: Zero Trust is not “set it and forget it.” Regularly review and refine your policies, conduct penetration tests, and stay updated on emerging threats. Automate responses where possible.
- Action: Schedule quarterly policy reviews. Conduct annual penetration tests. Automate alerts for policy violations.
Practical Tips for Startups:
- Leverage Existing Tools: Many cloud platforms (AWS, Azure, GCP) offer native security features that align with Zero Trust. Maximize these before investing in new tools.
- Educate Your Team: Security is everyone’s responsibility. Train employees on Zero Trust principles, phishing awareness, and strong password practices.
- Start Small, Scale Gradually: Don’t try to implement everything at once. Prioritize the highest-risk areas and expand incrementally.
- Consult Experts: Consider bringing in a cybersecurity consultant with Zero Trust expertise, even for short-term guidance.
Real-World Impact & Case Studies
The impact of Zero Trust is best understood through its ability to prevent or significantly mitigate the fallout from real-world cyber incidents. While many companies don’t publicly detail their Zero Trust implementations, the philosophy has become a cornerstone for leading tech giants and innovative startups alike.
One of the most widely cited examples is Google’s BeyondCorp. Facing the challenge of securing its vast, globally distributed workforce and complex cloud infrastructure, Google pioneered many Zero Trust principles over a decade ago. Their approach eliminated the traditional corporate network boundary, treating all access requests as untrusted, regardless of whether they originated inside or outside Google’s physical offices. By implementing robust device and user verification, continuous authorization, and granular access controls, Google demonstrated that a truly perimeterless security model was not only feasible but superior. This model allowed their employees to work securely from anywhere, long before remote work became a global norm, proving its scalability and resilience.
Conversely, many high-profile breaches, such as the SolarWinds supply chain attack or various ransomware incidents targeting critical infrastructure, highlight the vulnerabilities of traditional security models. In these cases, initial access gained through a trusted vendor or a single compromised endpoint often allowed attackers to move laterally across networks, escalate privileges, and eventually reach critical systems or exfiltrate vast amounts of data. A Zero Trust architecture, with its emphasis on microsegmentation and continuous verification, would have significantly hampered such lateral movement, isolating the initial breach and limiting its blast radius. For instance, if the compromised SolarWinds software had been restricted to only communicate with specific, whitelisted internal resources through Zero Trust policies, its ability to spread and impact other systems would have been severely curtailed.
For startups, the lesson is clear: Zero Trust isn’t just for tech giants. Companies like Okta, a leading identity management provider, leverage Zero Trust internally to secure their own operations, demonstrating how a security-first mindset can be baked into the very fabric of a growing tech company. By adopting Zero Trust, these organizations are not just reacting to threats; they are proactively building resilient, adaptable security postures that protect their innovation and maintain customer trust in a hostile digital environment. It’s about preventing the headlines, not just responding to them.
FAQ: Zero Trust Security for Startups
Q1: Is Zero Trust only for large enterprises with massive budgets?
A1: Absolutely not. While large enterprises have the resources for comprehensive overhauls, the core principles of Zero Trust are highly beneficial and increasingly accessible for startups. Many cloud-native tools and SaaS solutions offer Zero Trust capabilities (e.g., ZTNA from Cloudflare or Zscaler, strong IAM from Okta) that are scalable and cost-effective for smaller organizations. Starting with strong MFA, endpoint security, and segmenting access to your most critical data can provide significant Zero Trust benefits without a “massive budget.”
Q2: What’s the biggest challenge for a startup in adopting Zero Trust?
A2: The biggest challenge is often the initial mindset shift and the complexity of identifying and mapping all critical assets and data flows across a dynamic, evolving startup environment. It requires a deep understanding of your infrastructure and data. Another challenge can be integrating disparate security tools and overcoming technical debt from legacy systems, even if minimal in a startup context. However, for cloud-native startups, this integration can be smoother.
Q3: How long does it typically take to implement a Zero Trust model?
A3: Zero Trust is a journey, not a destination. You can achieve significant gains in security posture within 3-6 months by focusing on key areas like MFA and endpoint security. A more comprehensive implementation involving extensive microsegmentation and policy refinement across all critical assets can take 1-2 years or more, evolving continuously. The key is to start with your “crown jewels” and expand incrementally.
Q4: What’s the difference between Zero Trust and a traditional VPN?
A4: A traditional VPN grants users access to the entire corporate network once authenticated, essentially extending the trusted perimeter to the user’s device. This allows lateral movement if the device or user is compromised. Zero Trust Network Access (ZTNA), a core component of Zero Trust, provides granular, direct-to-application access based on identity, device posture, and context. It doesn’t put users on the network; it connects them securely to specific applications, adhering to the principle of least privilege and eliminating implicit trust.
Q5: What are the absolute first steps a small startup should take towards Zero Trust?
A5: Start with these non-negotiables:
- Implement Multi-Factor Authentication (MFA) everywhere: Especially for all SaaS applications, cloud consoles, and internal tools.
- Adopt a robust Endpoint Detection & Response (EDR) solution: For all employee devices.
- Inventory your critical data and applications: Understand what needs protecting most.
- Enforce least privilege: Review user permissions and revoke unnecessary access.
These foundational steps will deliver immediate security improvements and lay the groundwork for a more comprehensive Zero Trust strategy.
Conclusion: Your Startup’s Future Depends on Zero Trust
In the dynamic digital economy of 2026, cybersecurity is no longer an afterthought; it’s a foundational element of business strategy, investor relations, and customer trust. The Zero Trust security model, with its unwavering commitment to “never trust, always verify,” offers the most robust and adaptable defense against the relentless tide of cyber threats. For ambitious startup founders, embracing Zero Trust isn’t just about compliance or mitigating risk; it’s about safeguarding your innovation, protecting your intellectual property, and building a resilient enterprise that can withstand the challenges of the modern threat landscape.
The journey to Zero Trust may seem complex, but by adopting a phased approach, prioritizing your most critical assets, and leveraging the powerful, scalable tools available today, your startup can establish a security posture that is both formidable and future-proof. Don’t wait for a breach to learn this lesson. Start building your Zero Trust foundation today, and secure your place in tomorrow’s economy.
“`json
{
“@context”: “https://schema.org”,
“@graph”: [
{
“@type”: “Article”,
“mainEntityOfPage”: {
“@type”: “WebPage”,
“@id”: “https://eamped.com/zero-trust-security-model-explained-2026”
},
“headline”: “Zero Trust Security Model Explained 2026: Your Startup’s Non-Negotiable Defense Strategy”,
“image”: [
“https://eamped.com/images/zero-trust-security-banner.jpg”,
“https://eamped.com/images/zero-trust-diagram.jpg”,
“https://eamped.com/images/startup-security-concept.jpg”
],
“datePublished”: “2026-01-01T08:00:00+08:00”,
“dateModified”: “2026-01-01T08:00:00+08:00”,
“author”: {
“@type”: “Person”,
“name”: “Eamped Tech Strategist”
},
“publisher”: {
“@type”: “Organization”,
“name”: “Eamped”,
“logo”: {
“@type”: “ImageObject”,
“url”: “https://eamped.com/images/eamped-logo.png”
}
},
“description”: “Discover why the Zero Trust security model is indispensable for startups in 2026. This comprehensive guide explains core tenets, benefits, implementation steps, and tools to protect your business from escalating cyber threats.”,
“articleSection”: [
“The Core Tenets of Zero Trust: Trust Nothing, Verify Everything”,
“Why Zero Trust is a Must-Have for Startups in 2026”,
“The Pillars of a Robust Zero Trust Architecture”,
“Implementing Zero Trust: A Phased Approach for Startups”,
“Real-World Impact & Case Studies”
],
“keywords”: “Zero Trust, Zero Trust Security, Cybersecurity 2026, Startup Security, Data Protection, Network Security, Cloud Security, IAM, MFA, EDR, ZTNA, Microsegmentation, Cyber Threats, Startup Founder Guide”
},
{
“@type”: “FAQPage”,
“mainEntity”: [
{
“@type”: “Question”,
“name”: “Is Zero Trust only for large enterprises with massive budgets?”,
“acceptedAnswer”: {
“@type”: “Answer”,
“text”: “Absolutely not. While large enterprises have the resources for comprehensive overhauls, the core principles of Zero Trust are highly beneficial and increasingly accessible for startups. Many cloud-native tools and SaaS solutions offer Zero Trust capabilities (e.g., ZTNA from Cloudflare or Z