In the dynamic and increasingly digitized landscape of 2026, small businesses stand at a critical juncture. While innovation and agility are their hallmarks, these very attributes can sometimes inadvertently expose them to significant cyber threats. The misconception that cybercriminals only target large corporations is a dangerous fallacy; in reality, small businesses, often with fewer resources and less sophisticated defenses, represent an attractive and vulnerable target. A single data breach can lead to severe financial losses, reputational damage, legal ramifications, and even the closure of the business. Therefore, understanding and implementing robust cybersecurity best practices is not merely an IT concern but a fundamental business imperative. This comprehensive guide from Eamped will walk you through the essential steps and strategies your small business needs to fortify its digital defenses and ensure long-term resilience in an ever-evolving threat environment.
Understanding the Evolving Threat Landscape for Small Businesses
The digital world, while offering unprecedented opportunities for growth and customer engagement, also presents a complex array of threats that small businesses must navigate. Unlike larger enterprises with dedicated security teams and extensive budgets, small businesses often operate with limited resources, making them particularly susceptible to cyberattacks. The motivations behind these attacks range from financial gain through ransomware and data theft to industrial espionage, or simply the disruption of services. Understanding the specific nature of these threats is the first step toward building an effective defense.
Why Small Businesses Are Prime Targets
- Perceived Weaknesses: Cybercriminals often view small businesses as “soft targets” due to a lack of advanced security infrastructure, limited IT staff, and less stringent security policies compared to larger companies. They are betting on the fact that you might not have the sophisticated tools or expertise to detect and repel an attack quickly.
- Access to Larger Networks: Small businesses are frequently part of the supply chain for larger corporations. Attacking a smaller vendor can provide a backdoor into a bigger, more lucrative target. This “supply chain attack” model is becoming increasingly prevalent.
- Valuable Data: Even small businesses handle sensitive information, including customer data (names, addresses, credit card details), employee records, intellectual property, and financial information. This data is highly coveted on the dark web.
- Resource Constraints: Many small businesses lack the budget for premium cybersecurity solutions or dedicated security personnel, making them rely on basic, often insufficient, protections.
Common Cyberattack Vectors
- Phishing and Social Engineering: These remain among the most common and effective attack methods. Phishing emails, often disguised as legitimate communications from banks, vendors, or government agencies, trick employees into revealing credentials or clicking malicious links. Social engineering tactics manipulate individuals into performing actions or divulging confidential information.
- Malware and Ransomware: Malware (malicious software) can range from viruses and worms to spyware and adware. Ransomware, a particularly destructive form of malware, encrypts a victim’s files and demands a ransom, usually in cryptocurrency, for their release. The impact of a ransomware attack can be devastating, halting operations and leading to significant financial losses.
- Business Email Compromise (BEC): This sophisticated scam targets businesses that conduct wire transfers and have suppliers abroad. Attackers compromise legitimate business email accounts through phishing or malware and then impersonate employees to trick other employees, customers, or vendors into sending money to fraudulent accounts.
- Insider Threats: While often unintentional, employees can pose a significant security risk. This could be due to negligence (e.g., losing a company laptop, falling for a phishing scam) or, in rare cases, malicious intent.
- Unpatched Software Vulnerabilities: Software and operating systems often contain vulnerabilities that attackers can exploit. If patches and updates are not applied promptly, these vulnerabilities remain open doors for cybercriminals.
The Real Cost of a Breach
The financial and reputational fallout from a cyberattack can be catastrophic for a small business. Beyond immediate monetary losses from ransoms or data recovery efforts, there are significant indirect costs:
- Operational Disruption: Downtime, inability to access systems, and loss of productivity can grind business operations to a halt.
- Reputational Damage: Customers lose trust in businesses that fail to protect their data, leading to customer churn and difficulty attracting new clients.
- Legal and Regulatory Fines: Depending on the type of data compromised and the jurisdictions involved, small businesses may face hefty fines under regulations like GDPR, CCPA, or industry-specific compliance mandates.
- Investigation and Recovery Costs: Hiring forensic experts, rebuilding systems, and implementing new security measures can be extremely expensive.
- Loss of Intellectual Property: Trade secrets, proprietary designs, and other valuable intellectual property can be stolen, undermining competitive advantage.
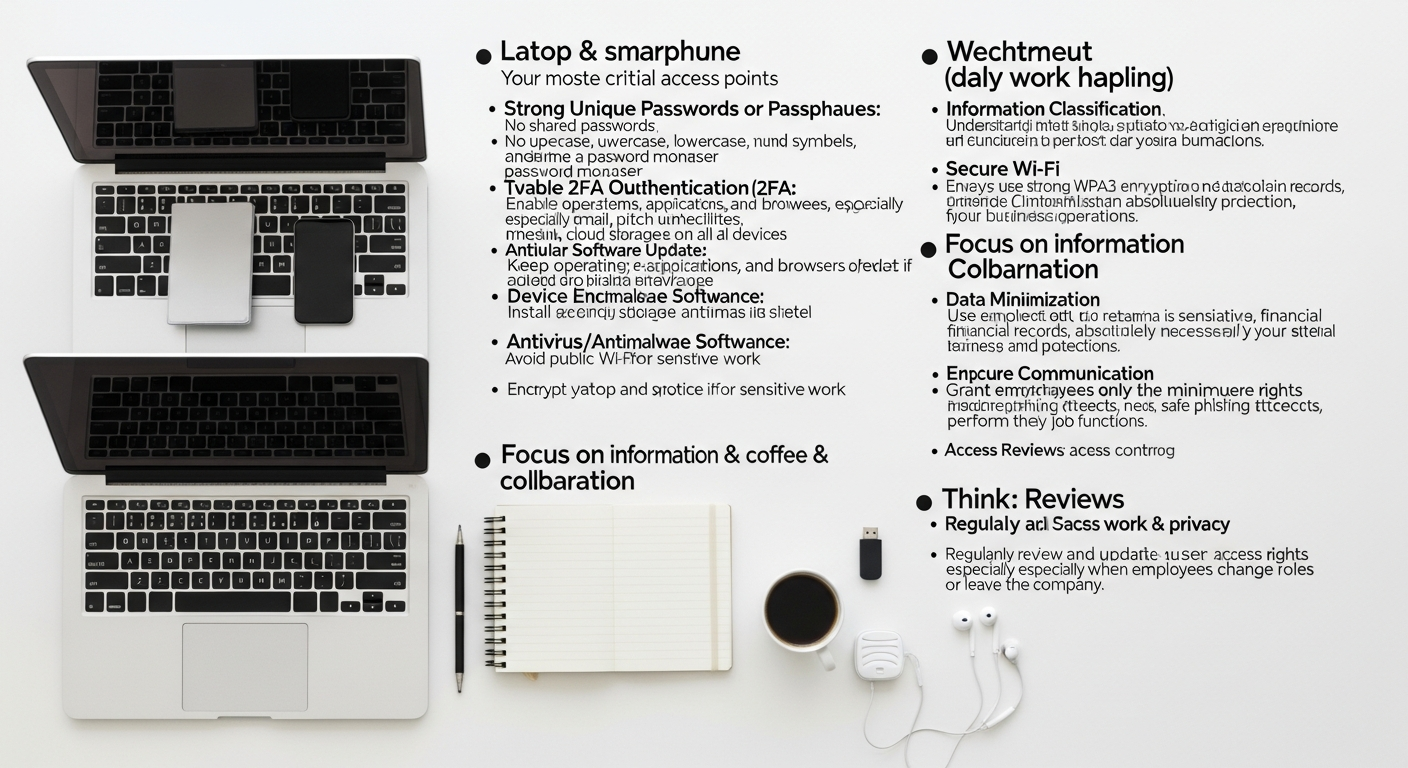
Foundational Security Measures: The First Line of Defense

Establishing a strong security foundation is paramount for any small business. These foundational practices are often cost-effective and provide a significant barrier against the majority of common cyber threats. Implementing these measures systematically can dramatically reduce your attack surface and enhance your overall security posture.
Strong Passwords and Multi-Factor Authentication (MFA)
Passwords remain the gatekeepers to your digital assets. Weak or reused passwords are an open invitation for attackers. The year 2026 demands a sophisticated approach to credential management.
- Password Policies: Enforce strong, unique passwords for all accounts. Policies should mandate a minimum length (e.g., 12-16 characters), a mix of uppercase and lowercase letters, numbers, and special characters. Avoid easily guessable information like birthdays or common words.
- Password Managers: Encourage or mandate the use of reputable password managers (e.g., LastPass, 1Password, Bitwarden). These tools generate and store complex, unique passwords for each service, reducing password fatigue and the risk of reuse.
- Multi-Factor Authentication (MFA): This is arguably the single most effective defense against unauthorized access. MFA requires users to provide two or more verification factors to gain access to an account (e.g., something you know like a password, something you have like a phone or hardware token, something you are like a fingerprint). Implement MFA for all critical systems, email, cloud services, and employee access. Even if a password is stolen, MFA prevents unauthorized access.
Regular Software Updates and Patch Management
Software vulnerabilities are a constant reality. Vendors regularly release patches to fix these flaws. Delaying these updates leaves your systems exposed.
- Automate Updates: Where possible, enable automatic updates for operating systems (Windows, macOS, Linux), web browsers, and critical business applications.
- Scheduled Patching: For systems where automatic updates are not feasible or require testing, establish a regular schedule for applying patches. This could be monthly or quarterly, depending on the criticality of the system and the severity of vulnerabilities.
- Third-Party Software: Don’t forget non-OS software. All applications, from your accounting software to your PDF reader, need to be kept up-to-date.
- Inventory Management: Maintain an accurate inventory of all software and hardware used within your business. This helps ensure that no system is overlooked during patching cycles. Just as you might track projects using the Best Project Management Software Startups offer, managing your software inventory and patch schedule requires a systematic approach.
Firewalls and Antivirus/Antimalware Solutions
These are fundamental layers of protection that every small business must have in place.
- Firewalls: A firewall acts as a barrier between your internal network and the internet, monitoring and controlling incoming and outgoing network traffic based on predetermined security rules. Ensure both network firewalls (for your router/gateway) and host-based firewalls (on individual computers) are enabled and properly configured.
- Antivirus and Antimalware: Install and maintain reputable antivirus/antimalware software on all endpoints (laptops, desktops, servers). These tools detect, prevent, and remove malicious software. Ensure they are configured to update automatically and perform regular scans. Consider advanced endpoint detection and response (EDR) solutions for greater threat visibility and response capabilities.
Secure Wi-Fi Networks
Your wireless network can be a significant vulnerability if not properly secured.
- Strong Encryption: Use WPA2 or, preferably, WPA3 encryption for your primary business Wi-Fi network. Avoid outdated and insecure protocols like WEP or WPA.
- Separate Networks: Create a separate Wi-Fi network for guests, completely isolated from your main business network. This prevents visitors from potentially accessing your internal resources.
- Strong Passphrases: Protect your Wi-Fi networks with long, complex passphrases, not just short passwords.
- Change Default Credentials: Always change the default username and password for your router and other network devices.
Protecting Your Data: Backup, Encryption, and Access Control
Data is the lifeblood of any modern business. Its loss or compromise can be devastating. Implementing robust strategies for data backup, encryption, and access control ensures the confidentiality, integrity, and availability of your most critical assets.
Data Backup Strategies: The Ultimate Safety Net
No security measure is foolproof. A reliable backup strategy is your last line of defense against data loss due to cyberattacks, hardware failure, natural disasters, or human error. The goal is to ensure you can quickly restore your operations.
- The 3-2-1 Rule: This widely recommended strategy dictates having:
- 3 copies of your data: The original and two backups.
- 2 different media types: For example, a local hard drive and cloud storage.
- 1 offsite copy: Stored physically in a different location or in a cloud service.
- Automated Backups: Implement automated backup solutions to ensure consistency and minimize human error. Schedule backups regularly (daily for critical data, weekly for less volatile information).
- Test Restores: Periodically test your backup and recovery process to ensure data integrity and that you can actually restore your systems when needed. Many businesses discover their backups are corrupted or incomplete only after a disaster strikes.
- Immutable Backups: For critical data, consider immutable backups, which cannot be altered or deleted once created. This is a powerful defense against ransomware, as encrypted data can be restored from an unaffected backup.
- Off-Network Backups: Ensure that at least one of your backup copies is physically or logically isolated from your primary network. This prevents ransomware from encrypting your backups along with your live data.
Data Encryption: Securing Data at Rest and in Transit
Encryption transforms data into an unreadable format, making it inaccessible to unauthorized individuals, even if they manage to gain access to the data itself.
- Encryption for Data at Rest:
- Full Disk Encryption (FDE): Enable FDE (e.g., BitLocker for Windows, FileVault for macOS) on all company laptops, desktops, and external drives. This protects data if a device is lost or stolen.
- Cloud Storage Encryption: Utilize cloud storage providers that offer server-side encryption and, where possible, implement client-side encryption before uploading sensitive data to the cloud.
- Database Encryption: For sensitive data stored in databases, implement database encryption or encryption at the application layer.
- Encryption for Data in Transit:
- SSL/TLS for Websites: Ensure your website uses HTTPS (SSL/TLS encryption) to secure communication between your website and visitors.
- VPNs for Remote Access: When employees access company resources remotely, they should use a Virtual Private Network (VPN) to create an encrypted tunnel, protecting data as it travels over public networks.
- Secure Email: Use email services that support encryption (e.g., PGP, S/MIME) for highly sensitive communications.
Access Management: The Principle of Least Privilege
Controlling who has access to what data and systems is a cornerstone of cybersecurity. The “Principle of Least Privilege” dictates that users should only be granted the minimum necessary access rights to perform their job functions.
- Role-Based Access Control (RBAC): Implement RBAC to assign permissions based on job roles rather than individual users. This simplifies management and reduces the risk of over-privileging users.
- Regular Access Reviews: Periodically review user accounts and their assigned permissions. Remove access for former employees immediately and adjust permissions for current employees whose roles have changed.
- Strong Administrator Controls: Treat administrator accounts with extreme caution. Use separate, dedicated administrator accounts for IT staff, and ensure these accounts are protected with strong MFA. Avoid using administrator accounts for daily tasks.
- Vendor and Third-Party Access: Carefully manage access granted to third-party vendors and contractors. Ensure contracts include security clauses and that access is revoked immediately upon project completion.
Data Loss Prevention (DLP)
DLP solutions monitor, detect, and block sensitive data from leaving your organization’s control. While often associated with larger enterprises, small businesses can benefit from simpler DLP features offered by some endpoint protection or cloud security solutions. This can prevent accidental or malicious sharing of sensitive customer or proprietary information.
Employee Training and Awareness: Your Human Firewall

Technology alone cannot secure your business. Your employees are both your greatest asset and your most significant vulnerability. A well-trained and security-aware workforce acts as a powerful “human firewall,” capable of detecting and thwarting many cyberattacks. Investing in regular cybersecurity training is one of the most cost-effective security measures a small business can undertake.
The Critical Role of Employee Awareness
Cybercriminals frequently target employees because it’s often easier to trick a human than to bypass sophisticated technical defenses. Phishing, social engineering, and malware delivery all rely on human interaction. When employees are educated, they become the first line of defense, capable of identifying suspicious activities and reporting them.
Key Training Topics and Best Practices
- Phishing and Social Engineering Recognition:
- Teach employees how to identify suspicious emails (e.g., generic greetings, urgent language, unusual sender addresses, grammatical errors, unsolicited attachments/links).
- Conduct simulated phishing campaigns to test employee vigilance and reinforce training. Provide immediate feedback and remedial training for those who fall victim.
- Educate on social engineering tactics like pretexting, baiting, and quid pro quo, which can occur via email, phone calls, or even in person.
- Strong Password Hygiene and MFA Usage:
- Reinforce the importance of using strong, unique passwords and the benefits of password managers.
- Ensure all employees understand how to use MFA effectively and why it’s a critical security layer.
- Safe Browsing Habits:
- Instruct employees to be cautious about clicking on unknown links, especially those from untrusted sources.
- Advise against downloading unauthorized software or plugins.
- Explain the risks of public Wi-Fi and the importance of using a VPN when connecting to company resources from insecure networks.
- Data Handling and Confidentiality:
- Train employees on proper procedures for handling sensitive customer data, proprietary information, and company secrets.
- Emphasize the importance of secure document storage (physical and digital) and the risks of sharing confidential information through insecure channels.
- Device Security:
- Educate employees on securing company-issued devices (laptops, smartphones) with strong passcodes and encryption.
- Explain policies regarding personal device usage (BYOD – Bring Your Own Device) and the risks associated with mixing personal and business data.
- Stress the importance of reporting lost or stolen devices immediately.
- Incident Reporting Procedures:
- Establish clear, easy-to-understand procedures for reporting any suspected security incidents, no matter how small.
- Emphasize that there will be no punitive action for reporting an honest mistake, as quick reporting is crucial for containment.
- Provide clear contact points for security concerns.
Regular Refreshers and Ongoing Education
Cyber threats evolve constantly, so training should not be a one-off event. Implement a continuous training program with:
- Annual Mandatory Training: Comprehensive training sessions covering all essential topics.
- Quarterly or Bi-Annual Micro-Training: Short, focused modules on specific topics or emerging threats.
- Security Awareness Campaigns: Regular reminders, newsletters, posters, or intranet messages about current threats and best practices.
- Leadership Buy-in: Ensure management actively participates in and champions cybersecurity training, setting an example for the entire organization.
Incident Response Planning: When the Unthinkable Happens
No matter how robust your defenses, the reality is that a cyberattack is not a matter of ‘if,’ but ‘when.’ A well-defined incident response plan (IRP) is crucial for minimizing the damage, recovering quickly, and ensuring business continuity. For a small business, this plan doesn’t need to be overly complex, but it must be actionable and understood by key personnel. Just as a business might use the Best Project Management Software Startups to meticulously plan product launches, an incident response plan requires careful organization and task management.
Why an Incident Response Plan is Essential
- Minimize Damage: A clear plan enables a swift and coordinated response, limiting the scope and impact of an attack.
- Faster Recovery: It provides a roadmap for restoring systems and data, reducing downtime and business disruption.
- Compliance and Legal Protection: Demonstrates due diligence and can help meet regulatory requirements for breach notification.
- Maintain Trust: A professional response helps preserve customer and partner trust, even after an incident.
- Learn from Experience: The post-incident review process helps identify weaknesses and improve future defenses.
Key Components of a Small Business IRP
While an IRP can be detailed, even a simplified version for a small business should address these core phases:
1. Preparation: Before the Attack
- Form an Incident Response Team: Identify key individuals (e.g., IT lead, business owner, legal counsel, communications lead). Assign clear roles and responsibilities. Even if it’s just one or two people, define who does what.
- Develop Communication Protocols: How will the team communicate during an incident if regular channels are compromised? (e.g., secure messaging apps, out-of-band communication).
- Gather Critical Information: Maintain an inventory of all assets (hardware, software, data), network diagrams, and contact information for vendors, ISPs, and legal counsel.
- Regular Backups: Ensure your data backup strategy is robust and regularly tested, as discussed earlier.
- Tabletop Exercises: Periodically run through a simulated incident to test the plan and identify gaps.
2. Identification: Detecting the Incident
- Monitoring: Implement basic monitoring of network traffic, server logs, and security alerts from antivirus/firewall solutions.
- Employee Reporting: Train employees on how to recognize and report suspicious activities promptly.
- Clear Reporting Channels: Ensure employees know exactly who to contact and how to report a potential incident.
3. Containment: Limiting the Damage
- Isolation: Quickly isolate affected systems or networks to prevent the spread of the attack. This might involve disconnecting compromised devices or segments.
- Evidence Preservation: Take steps to preserve forensic evidence for later analysis (e.g., system images, logs).
- Short-Term Measures: Implement immediate actions to stop the attack, such as disabling compromised accounts or blocking malicious IP addresses at the firewall.
4. Eradication: Removing the Threat
- Root Cause Analysis: Determine how the attacker gained access and what vulnerabilities were exploited.
- Threat Removal: Clean infected systems, remove malware, patch vulnerabilities, and rebuild compromised systems if necessary.
- Password Resets: Force password resets for all potentially compromised accounts.
5. Recovery: Restoring Operations
- System Restoration: Restore data from clean backups and bring systems back online in a controlled and secure manner.
- Verification: Thoroughly test systems to ensure they are fully functional and free of any lingering threats.
- Monitoring: Increase monitoring for a period to detect any recurrence of the attack.
6. Post-Incident Review: Learning and Improving
- Lessons Learned: Conduct a thorough review of the incident. What happened? How well did the plan work? What could be improved?
- Actionable Insights: Document findings and implement necessary changes to your security policies, procedures, and technical controls. This iterative process is crucial for continuous improvement.
- Communication Review: Evaluate how internal and external communications were handled.
Communication Strategy During an Incident
Clear and timely communication is vital. Your plan should outline:
- Internal Communication: Who needs to know, and when? How will employees be updated?
- External Communication:
- Customers: When and how will affected customers be notified? Prepare clear, concise messages.
- Partners/Vendors: Inform relevant business partners whose systems or data might be affected.
- Regulators/Law Enforcement: Understand your legal obligations for breach notification and contact relevant authorities if required.
- Public Relations: Have a plan for managing public perception and media inquiries.
Leveraging Technology and Professional Expertise
While foundational practices and employee training are critical, small businesses can further bolster their defenses by strategically adopting certain technologies and, when appropriate, seeking external professional expertise. This doesn’t necessarily mean a massive budget overhaul, but rather smart investments that yield significant security benefits. Understanding How To Choose Business Intelligence Tool to gain market insights can be analogous to selecting the right security tools – both require careful evaluation of needs, capabilities, and scalability.
Security Information and Event Management (SIEM) Light
Traditional SIEM solutions can be complex and expensive for small businesses. However, scaled-down or cloud-based versions can provide valuable centralized logging and alert capabilities. These tools aggregate security logs from various sources (firewalls, servers, endpoints) and use analytics to detect suspicious patterns that might indicate an attack. Even a simplified SIEM can provide crucial visibility, making it easier to identify threats that might otherwise go unnoticed.
Managed Security Service Providers (MSSPs)
For many small businesses, maintaining an in-house cybersecurity expert or team is financially unfeasible. This is where an MSSP becomes invaluable. An MSSP offers outsourced monitoring and management of security devices and systems. They can provide:
- 24/7 Monitoring: Round-the-clock surveillance of your network and systems for threats.
- Threat Detection and Response: Expertise in identifying and responding to incidents, often faster and more effectively than an internal team.
- Vulnerability Management: Regular scanning for vulnerabilities and recommendations for remediation.
- Compliance Assistance: Help in navigating regulatory requirements.
- Cost-Effectiveness: Access to enterprise-grade security expertise and tools at a fraction of the cost of building an in-house team.
Choosing the right MSSP requires due diligence, similar to evaluating the Best Project Management Software Startups or any other critical business partner. Look for providers with experience serving small businesses, clear service level agreements (SLAs), and strong references.
Cloud Security Considerations
Small businesses increasingly rely on cloud services (SaaS, IaaS, PaaS) for everything from email to data storage and application hosting. While cloud providers offer significant security advantages, it’s crucial to understand the shared responsibility model:
- Provider’s Responsibility: The cloud provider is generally responsible for the security of the cloud (e.g., infrastructure, physical security, hypervisor).
- Your Responsibility: You are responsible for security in the cloud (e.g., data, applications, operating systems, network configuration, access management).
- Best Practices:
- Strong Configuration: Properly configure security settings within your cloud services (e.g., S3 bucket policies, Azure/AWS security groups). Misconfigurations are a leading cause of cloud breaches.
- MFA for Cloud Accounts: Always enable MFA for all cloud administrator and user accounts.
- Data Encryption: Utilize encryption offered by cloud providers for data at rest and in transit.
- Cloud Access Security Brokers (CASBs): Consider CASBs for enhanced visibility and control over cloud application usage and data flow.
- Regular Audits: Periodically review your cloud security configurations and access logs.
Endpoint Detection and Response (EDR)
Traditional antivirus is foundational but often not enough against sophisticated, file-less, or zero-day attacks. EDR solutions go beyond simple signature-based detection, continuously monitoring endpoints for suspicious behavior, providing deeper visibility, and enabling faster response to threats. Many modern antivirus solutions now incorporate EDR capabilities, making them more accessible for small businesses.
Staying Ahead: Future-Proofing Your Cybersecurity Strategy
Cybersecurity is not a static endeavor; it’s a continuous process of adaptation and improvement. In 2026, the threat landscape will continue to evolve rapidly, requiring small businesses to be proactive in their defense strategies. Future-proofing your cybersecurity involves regular assessments, strategic budgeting, and a commitment to continuous learning.
Regular Security Audits and Penetration Testing
Just as you’d regularly audit your financials, your cybersecurity posture needs periodic assessment. This helps identify vulnerabilities before attackers do.
- Vulnerability Assessments: These scans identify known weaknesses in your systems, networks, and applications. They provide a prioritized list of vulnerabilities to address.
- Penetration Testing (Pen Testing): A more active assessment where ethical hackers (pen testers) simulate real-world attacks to find exploitable vulnerabilities. This can be more expensive but provides a deeper understanding of your actual defenses. For small businesses, consider targeted pen tests on critical systems rather than full-scope engagements initially.
- Web Application Security Testing: If you have a customer-facing website or web applications, regular security testing is crucial to prevent common attacks like SQL injection or cross-site scripting.
- Third-Party Reviews: Engage reputable third-party security firms for these audits to get an objective perspective on your security health.
Compliance and Regulatory Adherence
Depending on your industry and the data you handle, you may be subject to various compliance mandates. Failure to comply can lead to significant fines and reputational damage.
- Understand Your Obligations: Research and understand which regulations apply to your business (e.g., GDPR for EU customer data, CCPA for California residents, HIPAA for healthcare information, PCI DSS for credit card processing).
- Implement Controls: Design your cybersecurity practices to meet these regulatory requirements. This often aligns well with general best practices.
- Documentation: Maintain clear documentation of your security policies, procedures, and controls to demonstrate compliance.
Threat Intelligence Integration
Staying informed about emerging threats, vulnerabilities, and attack techniques can help you anticipate and prepare for future attacks. While large enterprises have dedicated threat intelligence teams, small businesses can leverage:
- Industry-Specific Feeds: Subscribe to threat intelligence feeds relevant to your industry.
- Security News and Blogs: Follow reputable cybersecurity news outlets and blogs (like Eamped!) to stay updated.
- Vendor Alerts: Pay close attention to security advisories and patches released by your software and hardware vendors.
- Government Resources: Agencies often provide free resources and alerts on current threats.
Understanding how cybercriminals conduct their campaigns, much like analyzing the effectiveness of What Is Pay Per Click Advertising campaigns, can provide valuable insights into their targeting methods and help you refine your defenses.
Budgeting for Cybersecurity
Cybersecurity is an ongoing investment, not a one-time expense. Allocate a dedicated budget for security that covers:
- Software and Hardware: Antivirus, firewalls, backup solutions, MFA tokens, EDR.
- Professional Services: MSSPs, auditors, pen testers, incident response retainers.
- Training: Employee security awareness programs.
- Insurance: Consider cyber insurance to mitigate financial losses from data breaches and other cyber incidents. Ensure you understand what your policy covers.
Treat cybersecurity budgeting as an essential operational cost, similar to rent or utilities, rather than a discretionary expense. The cost of prevention is almost always significantly lower than the cost of recovery from an attack.
Cultivating a Security-First Culture
Ultimately, the most resilient cybersecurity strategy is one that is embedded into the very culture of the organization. From the top down, every employee should understand their role in protecting the business’s digital assets. This involves:
- Leadership Commitment: Management must champion cybersecurity as a core business value.
- Continuous Improvement: Recognize that cybersecurity is an iterative process. Learn from incidents, adapt to new threats, and continuously refine your defenses.
- Open Communication: Foster an environment where employees feel comfortable reporting security concerns without fear of reprisal.
By implementing these advanced strategies and fostering a robust security culture, small businesses can move beyond basic protection and establish a truly resilient cybersecurity posture, ready to face the challenges of 2026 and beyond. Proactive steps today are the best defense against tomorrow’s threats, ensuring your business thrives securely in the digital age.
Frequently Asked Questions About Cybersecurity for Small Businesses
What is the single most important cybersecurity practice a small business should implement in 2026?
While many practices are crucial, implementing Multi-Factor Authentication (MFA) across all critical accounts (email, cloud services, internal systems) is arguably the single most impactful step
Recommended Resources
For more on cybersecurity best practices, see Accessibility In Ux Design Guide on Layout Scene.
Related reading: Best Home Office Setup Ideas 2026 (Bookmark Sharer).
From Our Network
- best free design tools for beginners 2025 (en Layoutscene)
- freelancer tools and apps to use in 2026 (en Bookmarksharer)