Modernizing the Monolith: A Definitive Guide to Integrating Legacy Systems with APIs
The tension between “what works” and “what is next” defines the current state of enterprise IT. For many organizations, the backbone of their operations—transaction processing, inventory management, or core banking—still resides in legacy systems. These systems are often decades old, written in COBOL or running on-premise mainframes, yet they contain the most valuable data the company owns. The challenge for today’s developers and architects is not just building new features, but ensuring these “monolithic anchors” can communicate with the modern ecosystem of SaaS, mobile apps, and AI-driven automation.
Integrating legacy systems with APIs (Application Programming Interfaces) is no longer an optional digital transformation project; it is a survival requirement. By 2026, the ability to expose legacy functionality through RESTful or GraphQL interfaces will separate agile enterprises from those buried under technical debt. This guide explores the architectural patterns, security considerations, and implementation strategies required to bridge the gap between yesterday’s infrastructure and tomorrow’s innovations.
The Challenge of the “Black Box”: Why Legacy Integration is Critical Today
Legacy systems are often described as “black boxes.” They are reliable and robust, but they are notoriously difficult to access. Most were built in an era of siloed computing, where the idea of a third-party application requesting data over the public internet was a security nightmare or a technical impossibility. These systems typically communicate via proprietary protocols, flat files, or direct database connections, making them incompatible with modern web standards.
The cost of maintaining these systems is high, but the cost of a “rip and replace” strategy is often higher. Total replacement introduces massive operational risk and astronomical expenses. Consequently, API integration becomes the middle ground. By wrapping legacy logic in a modern API, organizations can unlock data silos without disturbing the underlying stability of the system. This allows tech professionals to build automated workflows that trigger legacy actions—such as updating a 30-year-old ledger when a Shopify order is placed—creating a seamless experience for both employees and customers.
In the 2026 landscape, the rise of “Composable Architecture” demands that every piece of the tech stack be modular. If your core system cannot talk to a modern API gateway, it becomes a bottleneck that slows down the entire CI/CD pipeline. Integration is the only way to transform a static asset into a dynamic service.
Architectural Strategies: Choosing the Right Integration Pattern
There is no one-size-fits-all approach to legacy integration. The strategy you choose depends on the age of the system, the required latency, and the technical literacy of the team maintaining the legacy environment.
#
1. The Wrapper (Adapter) Pattern
This is the most common approach. You build a modern service—often using Node.js, Python, or Go—that sits in front of the legacy system. This “adapter” handles the translation. It receives a JSON request via a RESTful endpoint, translates it into a format the legacy system understands (like a specific SQL query or a terminal command), and then converts the response back into JSON.
#
2. API-Led Connectivity
Popularized by platforms like MuleSoft, this strategy involves three layers:
* **System APIs:** These provide a direct, raw interface to the legacy system.
* **Process APIs:** These combine data from multiple System APIs to create a business logic layer (e.g., “Check Customer Credit”).
* **Experience APIs:** These format the data specifically for the end-user device, whether it’s a mobile app or an internal dashboard.
#
3. The Sidecar Pattern
In a microservices environment, the sidecar pattern allows you to attach a modern communication layer to a legacy container or VM. The sidecar handles service discovery, logging, and security, allowing the legacy application to focus purely on its core logic while participating in a modern mesh network.
Bridging the Protocol Gap: Translating SOAP, COBOL, and Mainframes to REST
One of the steepest hurdles in legacy integration is the protocol mismatch. Modern web development is dominated by REST (Representational State Transfer) and JSON (JavaScript Object Notation). However, legacy systems often speak in SOAP (Simple Object Access Protocol), XML, or even binary formats.
To bridge this gap, developers must implement a robust mediation layer. If you are dealing with a SOAP-based service, tools like Apigee or Kong can act as a “SOAP-to-REST” transformer. These gateways ingest the WSDL (Web Services Description Language) file of the legacy service and automatically generate RESTful endpoints.
For even older systems, such as those running on IBM i or Z/OS, you may need to use Screen Scraping or Terminal Emulation APIs. While these are often considered “last resort” methods, modern RPA (Robotic Process Automation) tools have made this more reliable. The goal is to move away from these brittle connections toward “Data-at-Rest” integration, where you sync legacy databases to a modern cloud database (like PostgreSQL or MongoDB) in real-time, allowing the API to query the modern replica instead of the fragile original.
Security and Governance in a Hybrid Environment
When you expose a legacy system via an API, you are essentially opening a window into a house that may not have modern locks. Legacy systems were rarely designed with OAuth2, OpenID Connect (OIDC), or JWT (JSON Web Tokens) in mind. They often rely on hardcoded credentials or simple IP whitelisting.
The first rule of legacy integration is: **Never expose the legacy system directly to the public internet.**
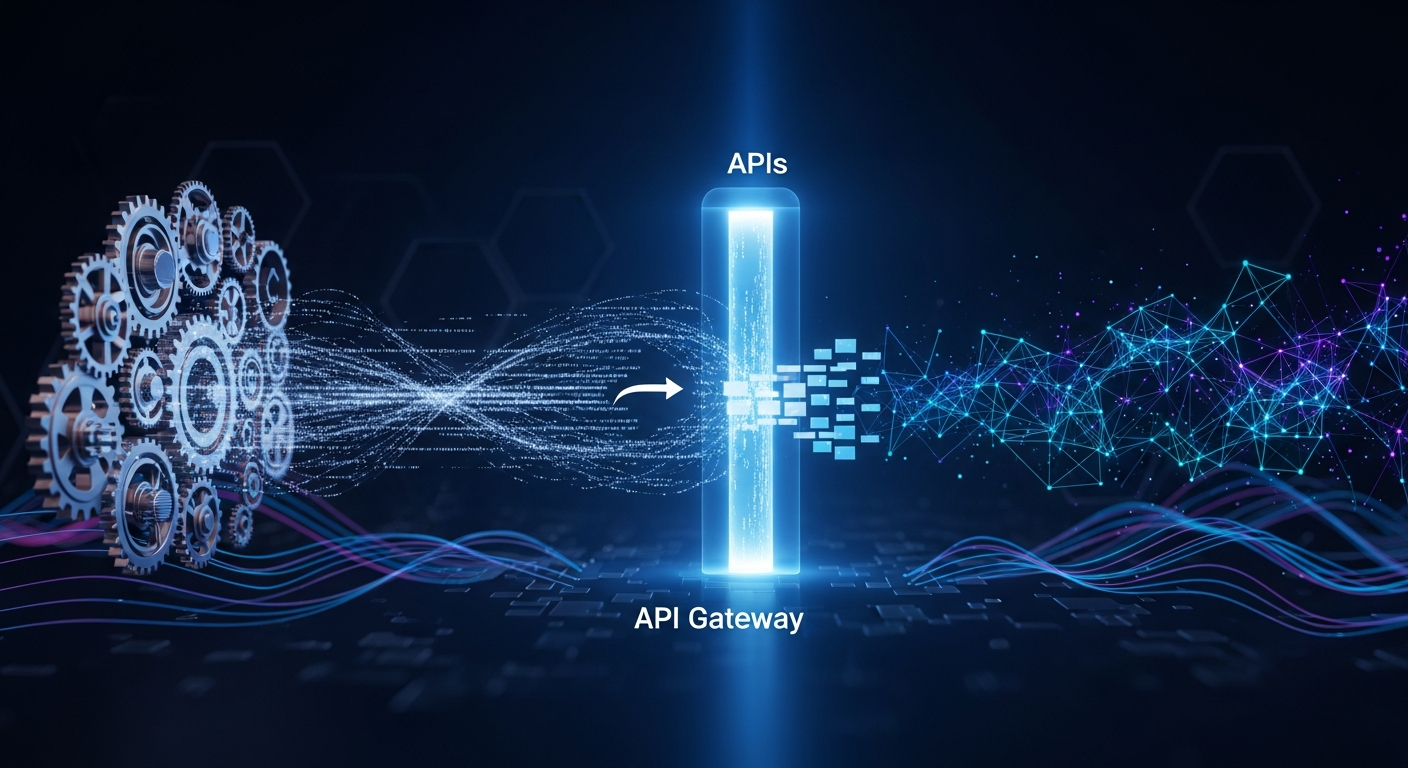
An API Gateway is mandatory. The gateway acts as a security enforcement point, handling:
* **Authentication and Authorization:** Validating modern tokens before the request ever touches the legacy hardware.
* **Rate Limiting and Throttling:** Legacy systems are easily overwhelmed by the high-volume traffic of modern web apps. A gateway ensures that a spike in mobile app usage doesn’t crash the mainframe.
* **Data Masking:** Ensuring that sensitive legacy data (like PII or unencrypted fields) is filtered or masked before being sent to the client.
Furthermore, implementing “Mutual TLS” (mTLS) between the API gateway and the legacy system ensures that the communication channel itself is encrypted, even if the legacy system’s internal protocols are insecure.
The Strangler Fig Pattern: A Roadmap for Incremental Migration
For tech professionals tasked with not just integrating but eventually replacing legacy systems, the “Strangler Fig” pattern is the gold standard. Named after a vine that grows around a tree and eventually replaces it, this pattern involves building new functionality in modern microservices while keeping the legacy system running.
The process works like this:
1. **Identify a small edge case:** Choose a minor function of the legacy system to migrate.
2. **Build a modern service:** Create an API-based service for that specific function.
3. **Redirect traffic:** Use a “Facade” or an API Gateway to route requests for that specific function to the new service, while all other requests continue to go to the legacy system.
4. **Repeat:** Slowly migrate more functions until the legacy system is no longer receiving traffic and can be decommissioned.
This approach minimizes risk because you are never doing a “Big Bang” migration. If the new API fails, you can quickly route traffic back to the legacy system. By 2026, this iterative approach will be the standard for high-availability environments where downtime is not an option.
Monitoring and Observability: Ensuring Reliability Beyond the Launch
An integration is only as good as its uptime. When you bridge two vastly different eras of technology, monitoring becomes complex. A failure in a modern UI might actually be caused by a timeout in a COBOL script four layers deep.
To maintain visibility, tech professionals must implement **Distributed Tracing**. Tools like OpenTelemetry allow you to attach a unique Trace ID to a request as it enters the API Gateway. Even as the request is translated and passed into the legacy environment, the Trace ID should persist (where possible) or be mapped to legacy logs.
Key metrics to track include:
* **Translation Latency:** How long is the middleware taking to convert JSON to XML?
* **Connection Pool Health:** Is the API exhausting the available connections to the legacy database?
* **Error Rate Mapping:** Translating obscure legacy error codes (e.g., “Return Code 12”) into meaningful HTTP status codes (e.g., 502 Bad Gateway) so that frontend developers can handle them gracefully.
FAQ
**1. What is the main difference between an ESB and an API Gateway in legacy integration?**
An Enterprise Service Bus (ESB) is typically used for complex, internal orchestration and protocol transformation (like MQ to SOAP). It is a “heavyweight” solution. An API Gateway is a “lightweight” edge service focused on security, rate limiting, and exposing services to the outside world. Modern integrations often use an API Gateway as the entry point, which then talks to an ESB or directly to the legacy system.
**2. Can I integrate a system that doesn’t have an existing network interface?**
Yes, though it is more difficult. If a system only accepts file-based inputs (like CSV drops), you can use an “Event-Driven Integration.” Your API receives a request, writes a file to a monitored directory (SFTP or S3), and a listener waits for the legacy system to output a result file, which the API then reads and returns to the user.
**3. Is REST always better than SOAP for legacy systems?**
For internal communication between two systems that already support SOAP, there is no need to switch. However, for any integration involving web browsers, mobile apps, or third-party developers, REST (or GraphQL) is superior due to its lower overhead and widespread library support.
**4. How do I handle slow response times from legacy hardware?**
The best approach is **Asynchronous Processing**. Instead of making the user wait for the legacy system to finish, the API returns a “202 Accepted” status and a job ID. The legacy system processes the request in the background, and the frontend either polls for the result or receives a webhook notification when it’s done.
**5. What are the biggest security risks when using APIs with legacy systems?**
The biggest risks are “Injection Attacks” (where modern input is used to exploit legacy command-line vulnerabilities) and “Insecure Direct Object References” (IDOR). Since many legacy systems lack granular row-level security, the API layer must be extremely strict about verifying that a user has the right to access the specific piece of data they are requesting.
Conclusion
Integrating legacy systems with APIs is the ultimate test of an IT professional’s architectural skill. It requires a deep respect for the stability of the past and a clear vision for the flexibility of the future. By using patterns like the Wrapper and the Strangler Fig, and by enforcing modern security standards via API gateways, organizations can turn their “technical debt” into a “technical foundation.”
As we look toward 2026, the goal of integration is not just to keep old systems alive, but to make them invisible components of a modern, automated workflow. When done correctly, the end-user will never know that the lightning-fast app in their hand is actually communicating with a mainframe in a basement three states away. That seamless connectivity is the hallmark of a successful digital transformation.